Secure Coding Training
Description
Learn about the most common security risks for web applications (OWASP Top 10). Find out how to identify and exploit general vulnerabilities in applications and how to fix existing holes and prevent new ones from occurring.
As an application developer, you are implicitly tasked with protecting your software against malicious hackers. To prepare you for battle, we will have you check a credit card transaction payment application for vulnerabilities and fix your findings in the program code as part of the "Secure Coding Training". You will get access to the following materials:
- Access to the source code of the payment application via GitBucket
- API documentation
- Secure code review checklist
- Security policy for software development
- Background story of the fictional company "Dubius Payment Ltd."
- Penetration test report of payment application
For the programming language, you can choose between PHP, Java, Python, Perl, Go, Ruby and Node.js. The payment application consists of 1000 to 2000 lines of code and uses the following frameworks:
| Languages | REST framework | OAuth2 framework |
|---|---|---|
| GO | Gorilla/Mux | Osin |
| Java | Spring | spring-security-oauth2 |
| NodeJS | Express | oauth2orize |
| PHP | Slim | slim-oauth2 |
| Python | Flask | Flask-OAuthlib |
| Ruby | Sinatra | simple_oauth2 |
| Perl | Mojolicious | OAuth2 Server Plugin |
What makes our training unique: We provide you with a fully-fledged laboratory environment - the test environment of "Dubius Payment Ltd.". As a fictitious payment service provider, Dubius Payment Ltd. offers merchants a payment application through which their customers can make credit card transactions: the payment gateway. For a sneak peek, we provided an excerpt of the REST API documentation here.
After a penetration test revealed several critical vulnerabilities in the payment gateway, it is your turn: As the newly hired team leader for software development, it is your job to check the source code of the application and eliminate all vulnerabilities. Practical training is a core part of our course. We created various vulnerability sets - each with ten vulnerabilities - of which you will be randomly assigned one when your lab time starts.
The lab is basically all yours - you will not be sharing it with anybody else. You get 20-day lab access. It is up to you when to use it. The laboratory environment is available around the clock.
After you buy a license for the course, you can access the course material and define the start date for your personal lab as well as the programming language. The 20 days start from the date you specify. You will get the following via our portal
- Access to the digital course materials
- Your OpenVPN access data for the development environment "Dubius Payment Ltd."
After successfully establishing a VPN connection, you will be able to access the source code of the payment gateway via GitBucket and make changes. Our documents will help you to understand how the payment system works and to carry out a structured secure code review. But because many roads lead to Rome, you are free to pick the technique with which you want to fix a vulnerability. Whether you were successful and whether the functionality of the application is ensured will be revealed by our functional tests and vulnerability scans, which you can trigger on our portal at any time.
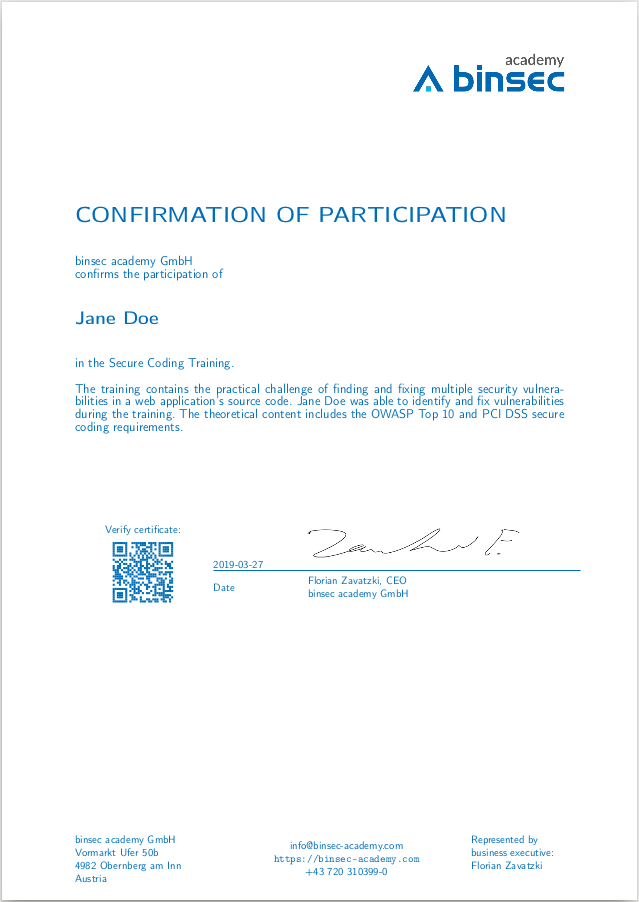
After your first successful fix of a vulnerability, you will get a confirmation of participation from us. You will be rewarded for your freestyle exercise with our Binsec Academy Certified Secure Coding Professional (BACSCP) certificate once you have eliminated eight out of the ten vulnerabilities that we included. However, we will only score your fixed vulnerabilities if all function tests of your last commit passed successfully.
After you have successfully fixed a vulnerability for the first time, you will automatically receive a PDF file that confirms your participation.
The BACSCP certificate will be sent to you by postal mail if you managed to eliminate eight out of a total of ten vulnerabilities by the end of your lab time. Please note that we will only rate the vulnerabilities fixed by you after all functional tests have been passed successfully in your last commit.
The BACSCP certificate shows third parties that you can
- identify the most common vulnerabilities in web applications and that you are capable of designing security solutions,
- securely develop a web application pursuant to OWASP and PCI DSS and
- carry out a secure code review in a structured manner.

You need a computer running Windows, macOS or Linux a s well as basic programming skills in one of the programming languages we support. In addition to the GIT tool, basic knowledge of this version of management software is also required - the commands "git clone", "git commit" and "git push" are sufficient. You can use any editor or IDE.
To connect to our lab, you need the open source software "OpenVPN". If you use a firewall that restricts outgoing data traffic, e.g. in a corporate network, you may need to enable (or have enabled) the associated TCP port. We will provide you with the port number together with the configuration file for your VPN. For technical reasons, this is not the default port of OpenVPN.
Video
FAQ
Below are the most common questions and answers about the course:
Tests have shown that professional software developers must invest at least 8 hours in the course or the laboratory. On average, we think that 12-16 hours is realistic. We recommend spreading those hours over the 20 lab days and/or adapting it to your pace of learning.
The payment application has been structurally kept simple. However, no above average code quality should be expected because it is basically a vulnerable software. But if you feel the need to refactor the source code, you are welcome to do so. In the end, only our function tests need to be successfull.


